Why Tiered Threat Intelligence Is the Missing Link in Modern Cybersecurity
January 20, 2026

Introduction: Why Knowing More Threats Has Not Made Organisations Safer
UK organisations are investing more in cybersecurity than ever before. Security stacks are growing. Logs are flowing. Dashboards are populated with indicators, alerts, and feeds from dozens of tools. Yet breaches continue to rise in frequency, speed, and impact.
Ransomware groups now operate like professional enterprises. Initial access brokers sell footholds at scale. Supply-chain compromise has become routine. Cloud adoption has erased traditional network boundaries. Regulatory scrutiny has intensified under frameworks such as NIS2 and DORA. At the same time, attackers have become faster, more patient, and more selective.
In this environment, many organisations believe they are “threat-informed”. They subscribe to feeds. They receive reports. They ingest indicators. But when incidents occur, a familiar question surfaces at board level:
“If we had threat intelligence, why didn’t we see this coming?”
The uncomfortable truth is that most organisations do not suffer from a lack of threat intelligence. They suffer from poorly structured intelligence. Data exists, but it does not consistently influence decisions, priorities, or outcomes.
This is where tiered threat intelligence becomes critical.
Tiered threat intelligence is not about buying more feeds or producing thicker reports. It is about structuring intelligence so that it reaches the right audience, at the right level, at the right time, and in a form that actually changes behaviour.
When done properly, tiered threat intelligence enables something most security teams aspire to but rarely achieve: predictive cybersecurity.
The Problem With Traditional Threat Intelligence
Intelligence Without Context Creates Noise
Many organisations treat threat intelligence as a technical input rather than a strategic discipline. Indicators of compromise are ingested into SIEM platforms. Feeds are correlated against logs. Alerts are generated. Analysts investigate.
What is missing is context.
An IP address means very little without understanding who is using it, why, how, and whether it aligns with threats that matter to the organisation. Without this context, intelligence becomes indistinguishable from noise.
This is why many SOC teams experience alert fatigue despite having “good intelligence”. The problem is not quantity. It is relevance.
Point-in-Time Intelligence Cannot Keep Up
Another limitation of traditional threat intelligence is timing. Intelligence is often consumed as a snapshot: a weekly report, a monthly briefing, or an annual threat review.
Attackers do not operate on these cycles.
Infrastructure changes daily. New vulnerabilities emerge continuously. Adversaries adapt techniques in real time. Intelligence that is not continuously refreshed and reassessed rapidly loses value.
Cyber risk is not static. Intelligence consumption should not be either.
Intelligence Often Stops at the SOC
In many organisations, threat intelligence is confined to technical teams. Boards receive high-level risk statements. Executives see red-amber-green charts.
Operational teams receive alerts. But there is rarely a shared intelligence narrative that connects business risk, attacker intent, and defensive action.
As a result, intelligence fails to influence investment decisions, exposure prioritisation, or operational readiness.
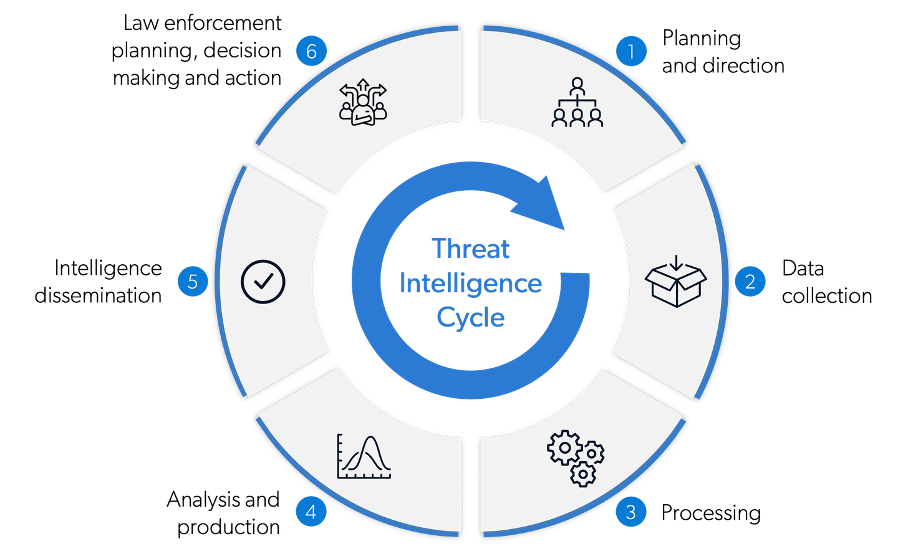
What Is Tiered Threat Intelligence?
Tiered threat intelligence is a structured approach that recognises a simple reality:
Different stakeholders need different intelligence.
A board member does not need indicators. A SOC analyst does not need geopolitical analysis. A CISO needs both, but in different forms and at different times.
Tiered threat intelligence organises intelligence into distinct layers, each aligned to a specific audience and decision type. Together, these tiers form a continuous intelligence pipeline that supports strategic planning, operational readiness, and real-time defence.
Rather than producing “one report for everyone”, tiered intelligence ensures that intelligence is consumable, actionable, and measurable at every level of the organisation.
Strategic Threat Intelligence
Strategic Threat Intelligence
Audience: Board, executive leadership
Strategic threat intelligence focuses on long-term risk, trends, and business impact. It answers questions such as:
- Which threat actors are targeting our sector?
- How is the threat landscape evolving over the next 12–36 months?
- What regulatory, geopolitical, or economic factors increase our exposure?
- Where should we invest to reduce material risk?
This tier translates cyber threats into business language. It supports decisions around funding, insurance, mergers and acquisitions, and resilience planning. Importantly, it enables boards to understand why certain security investments are necessary, not just what they cost.
Without strategic intelligence, cyber risk discussions remain abstract and reactive.
Operational Threat Intelligence
Audience: CISOs, security leadership, risk owners
Operational threat intelligence bridges strategy and execution. It focuses on adversary capability, intent, and targeting patterns.
Key questions include:
- Which threat groups are actively targeting organisations like ours?
- What campaigns are currently underway?
- What initial access vectors are being exploited?
- How do these threats align with our environment and exposure?
This tier allows security leaders to prioritise controls, focus testing efforts, and align teams around the threats that genuinely matter. It directly informs incident response planning, tabletop exercises, and security architecture decisions.
Operational intelligence is where threat awareness becomes preparedness.
Tactical Threat Intelligence
Audience: SOC teams, detection engineers, security operations
Tactical intelligence focuses on how attacks happen. It includes attacker techniques, tools, and procedures, often mapped to frameworks such as MITRE ATT&CK.
This tier supports:
- Detection engineering
- Threat hunting
- Control validation
- Incident investigation
Tactical intelligence helps teams answer questions such as:
- How does this threat move laterally?
- What persistence mechanisms are used?
- Which detections are effective and which are blind?
When tactical intelligence is aligned with operational context, it allows teams to proactively hunt for attacker behaviour rather than waiting for alerts to trigger investigations.
Technical Threat Intelligence
Audience: Tools, automation, enrichment pipelines
Technical intelligence includes indicators such as IP addresses, domains, hashes, and signatures. On its own, this tier has limited value. Indicators change rapidly and are easily evaded.
However, when technical intelligence is contextualised by higher tiers, it becomes powerful. Indicators are no longer generic; they are prioritised based on relevance, likelihood, and impact.
This tier enables automation while avoiding the common pitfall of blind blocking and unnecessary disruption.
Why Tiered Threat Intelligence Enables Predictive Cybersecurity
Most security programmes are reactive by design. Alerts trigger investigations. Incidents trigger response. Lessons are learned after impact.
Tiered threat intelligence changes this dynamic.
By understanding adversary intent, targeting patterns, and preparatory behaviour, organisations can identify signals of attack planning before exploitation occurs.
Predictive cybersecurity does not mean predicting the exact time and method of an attack. It means narrowing uncertainty. It means knowing which threats are most likely, which weaknesses matter most, and which actions will meaningfully reduce risk.
In practical terms, this allows organisations to:
- Prioritise vulnerabilities that are actively exploited, not just high-scoring
- Focus detection on attacker behaviour that aligns with real threats
- Prepare response teams for the scenarios most likely to occur
- Allocate resources based on exposure, not assumption
Threat intelligence only matters if it changes what you do next. Tiered intelligence ensures that it does.
Real-World Scenario: From Alert Fatigue to Attack Prediction
Consider a mid-sized UK organisation operating a hybrid cloud environment. The security team receives thousands of alerts per day. Intelligence feeds are active. Yet incidents still occur with little warning.
Through tiered threat intelligence, the organisation identifies that several ransomware groups are actively targeting its sector using specific initial access techniques. Operational intelligence highlights a surge in credential-based access linked to cloud environments. Tactical intelligence maps the associated techniques to existing detection gaps.
Instead of responding to alerts in isolation, the organisation adjusts priorities:
- Identity controls are hardened
- Specific detections are engineered
- Incident response playbooks are updated
- Leadership is briefed on likely attack scenarios
Weeks later, suspicious activity is detected that aligns with known preparatory behaviour. The intrusion is contained before encryption or data exfiltration occurs.
The difference was not better tools. It was better intelligence structure.

How Tiered Threat Intelligence Strengthens MDR and CTEM
Managed Detection and Response without intelligence is reactive. Continuous Threat Exposure Management without intelligence is blind prioritisation.
Tiered threat intelligence enhances both.
For MDR, intelligence informs what to monitor, what to hunt, and what to escalate. Analysts are not simply responding to alerts; they are actively searching for behaviours aligned with known adversaries.
For CTEM, intelligence ensures that exposure reduction efforts focus on weaknesses attackers are actually exploiting. Rather than addressing every vulnerability equally, organisations reduce real-world exposure.
The result is a security posture that is continuously informed by the threat landscape, not periodically updated by compliance cycles.
Common Mistakes Organisations Make With Threat Intelligence
Despite good intentions, many programmes fail due to predictable issues:
- Treating intelligence as a product rather than a process
- Producing reports with no defined audience
- Measuring success by volume rather than impact
- Failing to integrate intelligence into decision-making
- Assuming automation can replace analysis
Tiered threat intelligence addresses these issues by design. It forces clarity around who intelligence is for and what it is meant to influence.
Building a Tiered Threat Intelligence Strategy
A mature tiered intelligence approach includes:
1. Defined intelligence consumers
Each tier has a clear audience and purpose.
2. Alignment to business risk
Intelligence is mapped to assets, services, and outcomes that matter.
3. Integration with security operations
Intelligence informs MDR, incident response, and exposure management.
4. Continuous refinement
Intelligence is assessed based on effectiveness, not volume.
This is not a one-off project. It is an ongoing discipline.
Why Intelligence-Led Security Is Becoming Non-Negotiable
Attackers are not slowing down. AI is accelerating reconnaissance and exploitation. Regulatory scrutiny is increasing. Boards are being held accountable for cyber resilience.
In this environment, security programmes that rely solely on detection and response will always be one step behind.
Intelligence-led security, supported by a tiered approach, allows organisations to move first. It transforms cybersecurity from a reactive function into a strategic capability.
Final Thoughts: From Knowing Threats to Staying Ahead of Them
Cyber threats are inevitable. Surprise does not have to be.
Tiered threat intelligence provides the structure needed to turn information into foresight. It enables organisations to anticipate, prioritise, and act with confidence.
Knowing threats is not enough.
Understanding, structuring, and using them effectively are what create resilience.
Ready to strengthen your security posture? Contact us today for more information on protecting your business.
Let's get protecting your business
Thank you for contacting us.
We will get back to you as soon as possible.
By submitting this form, you acknowledge that the information you provide will be processed in accordance with our Privacy Policy.
Please try again later.
Cybergen News
Sign up to get industry insights, trends, and more in your inbox.
Contact Us
Thank you for subscribing. It's great to have you in our community.
Please try again later.
SHARE THIS